1. Foreword: why you need to read this.
2. Is there a brief history of the internet and the web?
3. What about email?
4. Connecting to the internet.
5. How do I set up my computer(s) for broadband?
6. How do I avoid getting viruses and spyware?
7. What web browser should I use?
8. What email program should I use?
9. How can you really maximize safety?
10. What about wireless in the home?
11. How about a concise summary?
12. Glossary: what are all those TLAs and FLAs?
13. Appendix: why do you need enough random access memory?
The target audience for this primer is the vast majority of computer users; namely, people who are mystified by computers, email, Windows, and the web, and who are concerned about computer viruses and malware and hackers. You are welcome to download it, edit it, and give it to your friends and family who are using (or wish to use) a high-speed connection to the internet.
Especially if you are using a computer with Windows, and to a lesser extent if you are using another operating system (such as Apple OS X), you need to be aware that the internet is a dangerous place and your computer is at risk, both from within (e.g., from the Microsoft software) and from without. The threats from the outside are well-known: hackers getting into your computer; viruses and worms sent to you by email or accidentally downloaded from web sites; malicious "adware" and "spyware," generically known as "malware," which, when downloaded from web sites, will essentially take over your computer; and "phishing" scams set up by con artists to fool you into giving personal information so that they can steal your money. The danger from within is due to the fact that the bad guys have designed their invasive programs to take advantage of security flaws in the software. If you're going to spend any time in this environment, you will need a survival manual to keep you safe.
This primer is that manual. It is intended to do four things:
For a summary of what to do, go here.
Note item (3) above. If you hire someone to set up your computer, chances are they are going to do things that will cause you repeated trouble. To give you a preview of what follows, here is what they are likely to do:
Why would an "expert" who has worked on Microsoft software upgrades make so many mistakes? Because they are following a prescription set up about 10 years ago, before broadband was widely used (except in large corporate intranets supported by hardware professionals), before hardware router/firewalls were cheap and easy to install, before high quality free browsers and email clients were available. They are living in the last century, in a world where the only things they think you need, besides an anti-virus utility, are the programs that come bundled with XP or Vista.
There are hundreds of thousands of people that make their living doing software installation and maintenance on Windows computers. To get a perspective on how big and lucrative this business is, consider that in the early 1990s, Xerox was spending over $500 million each year to have Electronic Data Services keep their 100,000 PCs working. That is about $5,000 per PC per year. The idea of configuring a Windows computer so that you can attach it to the internet and it will just work -- without maintenance -- would not have appealed to these software professionals, because it would have ended a business worth about $30 billion annually.
How will this affect you? You are likely to spend 100 or more hours each year on your computer. If you follow the canonical Microsoft prescription, you will spend some of those hours in frustration, and you are also likely to spend a lot of money having your "expert" keep the computer working: removing spyware, reinstalling XP or Vista, changing the settings on your software firewall, fiddling with your email program when it stops working, etc. This manual is written to allow you to set up a safe and essentially maintenance-free installation.
I am assuming that you are using a recent computer, either a PC with Windows or a Mac. Today you can buy today a dual core (2 processors), 2 GHz (2 billion cycles/second) for each processor, with Windows 7 loaded, with at least 300 GB (300 billion bytes) of disk storage, 3 GB (three billion bytes) or more of RAM (random access memory), a CD (compact disk) writer and reader, and wireless 50+ Mbps (megabit per sec) ethernet connectivity -- all for about $400. And you can get this either as a small deskside computer or as a laptop computer. The laptop computer has the screen built in, whereas for the deskside computer you need to buy a large monitor (about $150 for a 21-23 inch flat screen).
Consequently, if your computer has any one of these characteristics:
Finally, a note on memory and windows operating systems. Windows is so bloated that you need at least 3 GB of memory so that Windows 7 will work smoothly. Windows XP needed at least 1.5 GB. We won't even discuss Windows Vista, which was junk and fortunately has been replaced by Windows 7, which is by far the best the Microsoft has been able to come up with. I've added a somewhat technical explanation in an appendix at the end, if you want to read a bit about memory in the history of computers.
The internet is the basic backbone on which everything happens. Contrary to well-known claims, Al Gore did not invent it. It was invented with funding from ARPA in the 1960s, and improved in the 1970s at various research labs, including the Xerox Palo Alto Research Center, BBN (Bolt, Baranek and Newman) and Stanford University. The internet consists of computers that are connected together, each with a unique "internet address," which is a series of four numbers, each less than 256 and separated by a dot, such as 63.173.212.3. Programs were written so that computers could connect to each other, using their internet (IP) addresses. Two of the most important of these programs are ftp and telnet. ftp stands for "file transfer protocol"; it lets you tell some computer to transfer files to another one. telnet gives you a little terminal on your computer so that you can log in over the internet and work on another computer. Both are still in widespread use today.
Some computers on the internet have special jobs. For example, there are computers whose job is to route the data, which is sent in little packets of information, from one machine to another, typically going through many machines on the way. Some of these run DNS (Domain Name Service), which just translates "domain names", such as www.wyom.net, into the corresponding four number internet address.
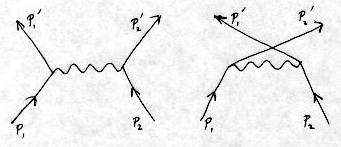
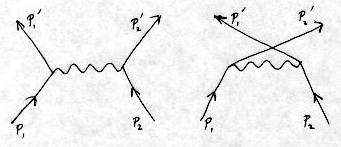
Scientists collaborating at different locations and using different machines needed better ways to transfer data, images and text. In 1991, Tim Berners-Lee at CERN (the European high-energy particle physics consortium in Geneva) invented one of the two most important applications on the internet: the World Wide Web (a.k.a. "WWW" or "Web"). There were three key ideas:
What do we mean by "download" and "upload"? The computers on the Web are not all "equal." Some are servers and the rest are clients. A server is a computer that will serve web pages to your computer when you ask for them. You computer is the client. When you go to www.google.com, the server at Google sends your web browser a page, which is actually a form. (It is a form because you can type text that can be uploaded back to the server.) Your browser downloads this page; you then type a query in a window, and upload the data back to Google's servers. These servers then find a set of URLs (links) that match your query, and send your browser (i.e., download to your browser) a new page, listing them. When you click on a link, your browser uploads the data associated with the request to the server that is holding it. There is enough information in the link so that your browser knows both the name of the server and the name of the specific piece of data, such as a photograph or article that you are requesting. The server could be anywhere on the planet, and it then downloads the requested page to your browser, which displays it in a (hopefully) readable format on your screen.
Berners-Lee also made a simple browser, but the first modern browser that displays images and marked-up text was made by a couple of people in Illinois who went on to found Netscape in 1994. The browsers we use today, such as Internet Explorer, Firefox, Safari and Google Chrome, are all descended from these first Netscape browsers.
Your ISP provides you with a number of mail boxes, each with a unique name of your choosing. Most ISPs provide two ways for you to get your email. The typical way is using a client email program, which they may provide. This program will download incoming mail from their server onto your computer, usually into a "folder" called "inbox." The email is downloaded from the server to your local machine automatically.
But suppose you are traveling and you don't have your computer. You can still read your email using the browser on any other computer that is connected to the internet. How? Your ISP provides a web address (like wyom.net) where you can log in and view and delete your mail. This web interface is different from your email client in an important respect: when you use a browser to view your email, it stays on the server. This would be a convenient alternative, except for one big problem: the program that your ISP provides for reading email from their server is lousy. You can use it in an emergency, but it is not a pleasant experience.
Google's Gmail solves this problem. It's a free web service that delivers your mail through your browser and keeps a copy on the server so that you have access to it any time and from any computer connected to the internet. With gmail, you don't need to have an email client on your machine. We'll discuss this in more detail later.
So the web and email are the two main reasons most people need a connection to the internet. But how do you get this connection?
Over 10 years ago, AOL and several other ISPs started a business that provided (1) internet connectivity over your telephone line (dial-up using a modem) and (2) a mailbox for your email. At that time, there were few alternatives.
But everything has changed since 1995. Today, most people can get a high-speed internet connection, also called broadband, in at least one of several ways. Download speeds are typically between 1 and 15 megabit/sec, which is many times faster than the 33.6 kilobit/sec rate of the modems. This factor of 30 to 500 is very important: among other things, it allows you to use graphical programs like Google Maps and Google Satellite interactively with fast response. Broadband can be delivered by:
Given the general availability of high-speed connections, what is the business model of AOL? Very simple: keep their 60 million or so accounts, bringing in $20/month each. But if you get broadband through your cable company, for example, and they give you more email accounts than you can use, why would you still pay AOL $20/month? AOL is no longer providing your internet connection, which was in any event abysmally slow. Sure, your friends know your email address at aol.com, and the lousy email client that AOL provides you is purposely crippled so that you can't export your address lists, if you've made them, to another email program. But that's a minor inconvenience. Here's the salient fact: once you have broadband, you have no use whatsoever for your previous dial-up ISP account. You should never need to use a klunky dial-up modem again!
In California, high-speed internet connection is about $40/month, through either DSL or Cable. Competition is slowly lowering the rates.
This little box can be purchased for between $20 and $50, and we can call it, as you might imagine, a router/firewall/4-port switch. There are several good brands. Be sure you get one that has wireless ethernet connectivity to your computers (as well as wired connectivity from the 4 ports). From here on I'm going to call the little box a "router," but keep in mind that it has several important functions, of which being a router is just one.
When you get Cable or DSL internet, you will need a high-speed modem. If they are going to charge you a monthly rental, it's usually cheaper to buy it. The input to this modem is your telephone line or your cable, and the output from the modem is an internet cable, which you can attach directly to your computer. But don't do that! There are many reasons not to connect your computer directly to the modem, and you already know one: you need a firewall. So you are going to get a router (which might be supplied free by your ISP), and the output of the modem goes into the router. This router will then talk to your computers (and printers), either through a wired connection or, most commonly now, wirelessly. (FYI, the wired connections are made by a special internet cable has connector jacks that look like wide telephone jacks. They have 8 wires, of which only 4 are typically used.)
Here's another reason to use the router. When you get a DSL modem, you will be given some software to install on your PC. SBC calls it "Enternet-100". This software is required to let your computer talk directly to the outside internet, but only if you don't have a router. With the router, all those functions are automatically taken care of, and you must not install any software from your broadband ISP. Repeat: Do not install any software from your broadband internet service provider! This is good: life gets simpler.
Actually it gets very much simpler. As I said, you plug your cable or DSL modem into your router. With a wireless connection, when you start your computer, it will automatically find the router, and once you sign in (wireless should always require a password; otherwise, your neighbors can use your connectin), your computer will automatically connect. With a wired connection, no password is required -- when your computer boots up, it will be connected to the internet (through the router and the modem).
If this is the first time you are turning on a computer, you will be asked a few questions by a "setup wizard", such as the name of the computer and the type of internet connection. For the latter, keep in mind that:
The router itself will need to be configured to work with your ISP. They will do this for you when they install your internet service. The router will almost always be configured to assign a local IP address to each of your computers (or network devices) as they are turned on. This dynamic configuration is called "DHCP".
Another important advantage of using a router with firewall is that you don't need to put special firewall software on your computer. This is not just a matter of convenience. In fact, it is important to avoid using all firewall software on your computer. This software, which you can get from various sources, the most notorious being ZoneAlarm, interacts badly with your most important internet programs; namely, your browser, your email and your anti-virus software. Norton and McAfee will try to sell you firewall software for your computer. Avoid it. Not using any firewall software will make your computer much easier to use.
Your router also has a web server built in, so you can see and change the settings using your browser. But as I said before, you shouldn't need to do this, because it will come configured to automatically handle your internet connection with maximum safety. (If you are curious, the typical local address of your router is 192.168.1.1, and you can go to your router by typing that into the address field of your browser. It will then display menus, such as the addresses of all the computers it is managing on the local area net. The local address it assigns your computer will be something like 192.168.1.100).
Viruses are pieces of code or programs that, when executed, can replicate themselves and send copies over the internet to other computers. Spyware is software, usually advertising-related, that is downloaded and sends information to another computer about what you are doing on your computer. Some spyware, which is also called adware, pops up annoying windows on your computer. Most spyware/adware has been so poorly designed that it essentially takes over the functioning of your computer, absorbing most of the computation cycles and slowing the computer to a crawl whenever you ask it to do something. Destructive variants of spyware, called "malware," overwrite minor system files and capture and send sensitive information, such as credit card numbers. You don't want to have any of this on your computer!
If you have an Apple, you probably don't need to worry about viruses, because there are (relatively) few Apple computers and, more importantly, the Apple operating system is much more secure than Windows. This is particularly true for Apple's newer Unix operating system, OSX. Linux and other variants of Unix are, so far, safe from all the common viruses.
Likewise, spyware mostly affects Windows computers. It has no effect on Unix. With Windows, the likelihood of infection is higher for two reasons: (1) the Microsoft Internet Explorer has a utility called ActiveX (a way of downloading and running programs, with insufficient security), and (2) the actual malware is tailored to run on Windows. So the rest of this section is for people using Windows on PCs. If you're running Apple OSX or Linux, you can skip the rest of this secdtion, unless you want to find out how much "fun" you are missing by using a relatively secure computer.
If you have a PC running Windows, there are several things that you should do to keep your computer "healthy." The most important is to install Norton Anti-Virus, which costs about $30. Once installed, Norton will automatically update itself periodically when you are connected to the internet. It will do this for one year after you purchase it, and you should renew the "subscription" each year. Norton will catch and isolate nearly every virus that comes to you as a mail attachment. But just get anti-virus from Norton.
By no means should you get McAfee's anti-virus software. McAfee is much more difficult to use than Norton, and it has been known to behave badly with other internet applications.
If for some reason you insist on using IE, be sure to turn off Microsoft's ActiveX software on the Internet Explorer (IE) browser, including all ActiveX "scripting" options. You'll find the ability to do this under the "Control Panel" and "Security". ActiveX allows someone to run programs on your computer, and these programs can be attached to email or downloaded from web sites by your browser. It is very dangerous. If you turn it off, a very small number of web sites will not work properly, but this is a small price to pay for the safety you get in exchange.
You should get in the habit of not opening email attachments about which you have any suspicions. Norton will catch most viruses, but it is best to stay alert. Viruses have become very sophisticated, and once they get in someone's computer, they will propagate by sending mail to everyone in that person's email contact list.
As mentioned above, a very important reason for not using Microsoft's IE browser is that only IE allows malware and spyware to be downloaded onto your computer. Spyware downloads became an epidemic starting as far back as 2004, and there are common versions that will steal nearly every computer cycle from your computer, so that it appears to slow to a crawl. If that happens, you have only two choices: try to remove it (which can be very hard) or re-install your Windows operating system. It's that bad! For a thorough review of what spyware is, how you get it, and how you get rid of it, see the Spyware/Adware/Malware FAQ and Removal Guide.
Here's a simple calculation. I would guess that spyware has afflicted at least 30% of all PCs. In the US alone, that amounts to perhaps 100 million. If each infection causes $300 loss in productivity and cost to remove it, we're looking at a loss of $30 billion. The problem is enormous, and it is way past time for the federal government to prohit the dissemination of spyware.
You should remember that nothing you do will keep you absolutely safe. Windows is so insecure, and there are so many people taking advantage of this, that new threats occur on a regular basis. Here's an example of a recent, serious problem. On December 29, 2005 it was reported that a security hole could result in arbitrary damage from a "wmf" type image that you receive by email or download from the web. A windows program automatically opens these images, which can contain programs that start running and literally take over your computer. Anti-virus software does not detect these trojan horses. It took Microsoft a week to put out a patch, which was a very short time by Microsoft standards, indicating the severity of the problem. The moral of this: keep your eyes open for reports of problems, don't open email attachments from sources you do not recognize, and let your computer download and install patches from Norton (anti-virus) and Microsoft, whenever they arrive. This is worth the risk, even though when Microsoft's Service Pack 2 was initially released, it was buggy and caused computers connected by local area networks to stop talking to each other.
And finally, we come to perhaps the biggest danger on the internet: a set of human-engineered traps that no software can save you from. These traps are emails (and associated web pages) that encourage you to give up passwords and other personal information such as credit card numbers. It's called {\it phishing\/}. The crooks are ingenious. For example, they might send you an official looking email saying that someone has attempted to break into your account and it is necessary to change your password. You are to go to a web site (by clicking on a link that looks perfectly good on the email) and supply your credit card number, your old (current) password, and a new password. Don't do it! No reputable establishment will ever send you such an email.
OK. We've established that there are three programs you must have if you are to use the internet. The first is a web browser, the second is an email client (although you can also use the web browser to get email), and the third is Norton Anti-Virus. In this section we discuss the browser, and in the next, your email client program.
As mentioned above, because of the security problems associated with the Microsoft IE browser, I recommend that the very first thing you do with IE is download Google Chrome, and then never use IE again. After the Chrome browser is downloaded, delete the IE shortcut icon so that you don't accidentally start it up. Check out the various functions available by clicking on the little wrench icon in the upper right corner. Security updates in the browser will be automatically downloaded to your computer, so you don't need to worry about keeping the version of Chrome up-to-date.
Thunderbird is a no-frills, lightweight open-source email program that comes from the same people (the Mozilla organization) that bring you the Firefox browser. Click here to get information and/or download Thunderbird. It comes with excellent anti-spam software and is easy to install. It has a utility to convert all your email addresses (the "address book") from your previous email client to Thunderbird.
By far, the best option for email is to use your browser with GMail, a web email server from Google, rather than a local email client like Thunderbird on your computer. Google's GMail service gives you up to 7600 Megabytes of storage (as of 2/09) at no cost. Your email is stored on Google servers and accessible from any computer that has a connection to the internet. Every word is indexed, so that you can input some words (as you do with a search engine) and instantly get a list of every email that has those words. This is a very convenient way to find some particular email. GMail now has the ability to download your mail locally, so that you can read it offline (i.e., when you're not connected to the internet)! It also has many advantages over a client that runs on a specific machine and downloads the mail off the server (i.e., removing it from the server):
Once you set up your gmail account, start playing with the email. The most important test is to send email to yourself and make sure that you receive it. You can also send yourself email with various attachments, such as jpeg images, html files, PDF files and plaintext files. What are these?
Attach each of these to a mail message, send it to yourself, and observe the way it appears when you receive it.
Before Google introduced GMail, you could get only about 4 Megabytes of storage on a free web mail service. GMail offers nearly 2000 times as much free storage. How is this possible? When the GMail server sends mail to your browser, Google will also put small advertisements related to your mail on the page. These ads are low-impact, like the ads Google puts on its search pages. You may not have even noticed them, sitting on the right hand side of the page. When you click on an ad, Google gets money from the advertiser, and that helps pay for your GMail service. After Google introduced GMail in April, 2004, with 1 Gigabyte of free storage, other companies suddenly decided to offer 100 Megabytes or more on web-based email clients. So free web-based email has suddenly become much more practical as an email option. At this time, GMail has perhaps 300 million users worldwide.
Suppose you already have email through an ISP. How much trouble is it to switch to using GMail? It turns out to be very simple. You get a GMail account, and then from GMail you tell your ISP to forward all email to your new GMail account. You also need to go to your ISP account (on the web) and turn off all spam filtering, so that the spam is also forwarded -- GMail can handle it better.
Note that in this process, you do not need to send an email to all your contacts explaining that your email address has changed. You can do this if you want, but because your ISP will now silently forward all email to your GMail account, you receive everything. And you can set up GMail to give either your old ISP address as the "sender" or your new GMail address. To set up forwarding, in GMail you go to "Settings", then "Account", and then set up forwarding from another account (your old ISP account). You'll need the password to that account, your old email address, and the POP server name and port number. For example, suppose your ISP is sbcglobal. You could set it up this way:
Email address: janedoe@sbcglobal.net
Username: janedoe@sbcglobal.net
POP Server: pop.att.yahoo.com
Port: 995
Label incoming messages: janedoe@sbcglobal.net (incoming to gmail)
Also:
Check the box: "Always use secure connection (SSL)"
And you probably want to say:
Always reply from default address (jane.doe@gmail.com)
That's all there is to it.
And, finally, we have saved the worst email client option for last. The winner for the worst email option is: Microsoft's Outlook Express, that comes with Windows. This is difficult to use, clunky and heavy-weight, and produces large files in a format that is not easily exported should you decide you want to use a better email client. So the advice here is not even to start with Outlook. Think of it as overweight application Windows bloatware, that you would do best to avoid.
Here's a real-life case. A friend of mine is an author, and she uses her computer ("Computer 1") for her writing. She wants maximum safety: reliable backup in case of hardware failure, no spyware to compromise Windows, no break-in from the internet. The works. She also needs to use email and e-commerce, and is willing to get a second computer ("Computer 2") to perform that function.
A consultant suggested that she completely isolate Computer 1, and burn CDs for backup and to transfer manuscripts to Computer 2. However, burning CDs is tricky and may be near the limit of my friend's ability to do it reliably.
Fortunately, there a simpler and more reliable way to meet her needs. Connect both computers to the internet through a router (with firewall and 4-port switch), with the firewall settings as they come from the manufacturer: all incoming ports closed. (You can only receive packets from outside the firewall from a server to which you have first established a connection, such as a web server at Google or Amazon.) We have covered this earlier -- no hacker can break through such a firewall. To meet the other two requirements, my friend gets a GMail account and sets her home page on Computer 1 to http://www.gmail.com. When going through the firewall to the internet, Computer 1 only goes to this page. Using Firefox, of course.
Then she uses her GMail account for exactly two functions: backup and communication with Computer 2. For backup, she attaches a chapter (or some other unit) to an email, and sends it to herself. The result is that the attachment is stored on Google's GMail server. This is a completely reliable method for backup, By contrast, if you burn a CD, it can get lost, destroyed, stolen, or be defective. Once the email has been sent, Computer 2 can retrieve it, and then send it through her ISP email account (e.g., sbcglobal) account to the outside world. The beauty of this method is that the GMail account is completely private. The only traffic to and from this account is hers.
She can also use a second GMail account, as the connection from Computer 2 to the outside world. This second GMail account is "public," in that it is used to send and receive email to the outside world. Then, when she backs up a chapter, she does it by attaching the chapter to a GMail send message on Computer 1, and sends it to both of her GMail account addresses (the secret one, and the public one). Computer 2 then uses the public GMail account to forward the data to the outside world. Computer 1 is completely isolated from the internet, except for the secret GMail account.
Why have these two accounts? If she used GMail to send directly from Computer 1 to the outside, people outside would find out about the secret GMail account (so it would no longer be "secret"), and they would send email back to it. Eventually viruses and other boolean pathogens may find their way to her secret GMail account. So the safest procedure is to completely quarantine the GMail account. With a secure (un-guessable) password, it would then have a level of security close to what can be achieved with physical isolation.
Used in this way, Computer 1 will not even require anti-virus protection. Computer 2, which is really out there on the internet, should have Norton anti-virus. If she uses an ISP email account, it will certainly receive spam, perhaps in part because her ISP email address was sold to bad guys, or a computer somewhere that has her email address in an address book was turned into a spam-mailing zombie, or some other nasty scenario. But even if Computer 2 is disabled by spyware, Computer 1 remains completely safe, along with all the backups on the GMail server.
Today, wireless networking in the home has become ubiquitous. All computers you get today are wireless. Many devices, such as printers, tablets and smart phones, have wireless internet connectivity. You can stream internet wirelessly to your HDTV using a $50 device. So it is important that your router is able to broadcast wirelessly. If your ISP brings you internet through cable or dish, they are likely to give you a wireless router by default. If not, ask for it. If your ISP is your phone company, your internet will come through DSL, and they may not provide a router. Wireless routers are not appreciably more expensive than routers that don't have it. All wireless routers also have wired connections, which can also be used.
Wireless has a limited range, so if your router is not "visible" everywhere in your house, you can get a wireless "repeater" or "range extender". You run an internet cable from your router to this repeater, and it talks to all devices within its range.
Your goal is to have a problem-free setup using the best application software for the most important applications, and at the lowest cost. We've outlined how you can do this for the most generally useful and important applications (the web and email). Once you have a satisfactory computer, there are only three steps:
And if you have a dialup ISP, removing it will save you half the cost of your broadband connection.
You can see how much memory you have by clicking on "System" in the Control Panel. In 2000, a computer with 128 MB of memory could squeak along running Windows 98. When XP came out, you needed at least 512 MB, and preferably 2 GB. If you don't have enough memory, it will take forever to boot up, and you'll hear the disk drive wildly seeking data to read. What is going on?
Ancient history. Computers before 1975 or so had a relatively small amount of memory, and they would typically run one program at a time. (The operating system was very small.) If your program didn't fit into the available memory, you needed to divide it up into pieces and tell the computer when to use each piece. But typically the operating system would read your program from disk into memory, and run it there. If your program was hogging the machine and another program couldn't fit in with it, the operating system would swap your program out and swap the other program in. In 1979, I remember watching an Interdata 8-32 computer, which cost about $250,000 and had only 4 MB of memory, swapping two programs that were compiling fortran. Each time a program would read in one line of source code to be compiled, it would get swapped out. The effect was comical -- that is, if you weren't waiting for your program to be compiled. In the late 1970s, virtual memory was implemented on Unix and other computers. Because it usually isn't necessary to have your entire program in memory at any time, the idea was to load only the parts of your program that were necessary into memory. The rest would stay on disk. The program was divided into pages, perhaps about 4 KB each, and they would be paged in when needed. Memory was a scarce resource, and this was a much more efficient use of memory. So typically your program would consist of some pages in memory and the other pages on the disk.
This isn't an ideal situation, because access to data on disk now takes about 5 milliseconds, whereas access to data in memory takes a few nanoseconds (a nanosecond is a thousandth of a millionth of a second). Thus, random access in memory can be up to a million times faster than finding something on the disk!
Your Microsoft OS (and all other operating systems) still have virtual memory -- they still page programs and data from the disk into RAM as needed. This is usually a good thing. If you have enough memory, a program gets loaded into memory, runs, and leaves. But if you don't have enough memory for all the programs you are loading to run (the OS itself, a browser, Norton, etc), chaos will ensue. To bring up the web browser, parts of the OS will get paged out. If too little of the OS is resident in memory, you get a situation where little pieces continually need to get paged back in, and other things are tossed out, as everything is fighting for memory. Disk paging is so slow that your computer essentially grinds to a halt.
My guideline is to have a minimum of 2 GB of memory for XP
and 3 GB for Windows 7. You can live with less, but everything is
significantly slowed down. And you really need this much memory
for programs that make heavy use of images, such as
Google Earth. With enough memory, everything will speed up
on your computer: booting, logging in and out, and launching programs.
It will allow you to run many different programs (such as email,
several browsers, a DVD movie, and a text editor) simultaneously.
It will greatly reduce wear and tear on your hard drive.
And it will allow you to store a lot of images in memory and run
great programs like Google Earth without annoying delays
due to memory paging.
